Table of Contents
- Abstract
- Linux Networking Term defined.
- Intro to Linux Networking
- How to Configure your network
- Network Manager on Ubuntu
- Networking on the Command line
- Is the network connected?
- OK I have an IP address do I have a route?
- I have a route, do I have a Name Server?
- How can I tell if I have any network cards available
- How can I set a static IP address for eth0
- How can I set a gateway IP address for eth0
- How to check if DNS is working
- How to check if you can access the internet
- Is the gateway computer alive
- Who owns that Internet name
- How fast is my network connection
- Example of a Packet transfer
- Linux Networking Books
Abstract
Networking in Linux is something we all use, but do we understand what is needed to make it work? Do we understand how to troubleshoot it when it doesn’t work? What happens when you only have a command line interface? I will attempt to give you both a mini course in networking and how to troubleshoot it in the process. Roll up your sleeves this talk is going to cover lots of details necessary for your Linux chops.
Linux Networking Term defined.
IP: An Internet Protocol address (IP address) is a numerical label assigned to each device (e.g., computer, printer) participating in a computer network that uses the Internet Protocol for communication. An IP address serves two principal functions: host or network interface identification and location addressing. Its role has been characterized as follows: “A name indicates what we seek. An address indicates where it is. A route indicates how to get there.” IP Address
IPv4: Internet Protocol version 4 (IPv4) is the fourth revision in the development of the Internet Protocol (IP) and the first version of the protocol to be widely deployed. Together with IPv6, it is at the core of standards-based internetworking methods of the Internet. As of 2012 IPv4 is still the most widely deployed Internet Layer protocol. IPv4 For those of you interested the next generation if IP addresses will be known as IPv6
Subnet Mask: A subnetwork, or subnet, is a logically visible subdivision of an IP network.[1] The practice of dividing a network into two or more networks is called subnetting. Subnet Mask
DNS: The Domain Name System (DNS) is a hierarchical distributed naming system for computers, services, or any resource connected to the Internet or a private network. It associates various information with domain names assigned to each of the participating entities. A Domain Name Service resolves queries for these names into IP addresses for the purpose of locating computer services and devices worldwide. By providing a worldwide, distributed keyword-based redirection service, the Domain Name System is an essential component of the functionality of the Internet. Domain Name Service
Gateway: The Gateway Address (or Default Gateway) is a router interface connected to the local network that is used to send packets out of the local network. Gateway Address
Network Interface: A network interface controller (also known as a network interface card, network adapter, LAN adapter and by similar terms) is a computer hardware component that connects a computer to a computer network. Network Interface Controller
Wired: A local area network that communicates over a wire, as opposed to a wireless network.
Static IP: A fixed IP address as opposed to a Dynamic IP address.
Wireless: A wireless local area network (WLAN) links two or more devices using some wireless distribution method (typically spread-spectrum or OFDM radio), and usually providing a connection through an access point to the wider internet. This gives users the mobility to move around within a local coverage area and still be connected to the network. Most modern WLANs are based on IEEE 802.11 standards, marketed under the Wi-Fi brand name. Wireless LAN
DHCP: The Dynamic Host Configuration Protocol (DHCP) is a network protocol that is used to configure network devices so that they can communicate on an IP network. A DHCP client uses the DHCP protocol to acquire configuration information, such as an IP address, a default route and one or more DNS server addresses from a DHCP server. The DHCP client then uses this information to configure its host. Once the configuration process is complete, the host is able to communicate on the internet. Dynamic Host Configuration Protocol
Wireless Security: Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is one of the least secure forms of security. A network that is secured with WEP has been cracked in 3 minutes by the FBI.[1] WEP is an old IEEE 802.11 standard from 1999 which was outdated in 2003 by WPA or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device which encrypts the network with a 256 bit key; the longer key length improves security over WEP. Wireless LAN Security
Intro to Linux Networking
As a starting point lets review a document from “The Linux Documentation Project” named Introduction to Linux/Networking for our introduction to Linux Networking.
When it comes to networking, Linux is your operating system of choice, not only because networking is tightly integrated with the OS itself and a wide variety of free tools and applications are available, but for the robustness under heavy loads that can only be achieved after years of debugging and testing in an Open Source project.
— The Linux Documentation Project Introduction to Linux/Networking
How to Configure your network
Network Manager on Ubuntu
We are going to start by looking at the network manager from Ubuntu 12.04 as a starting point.
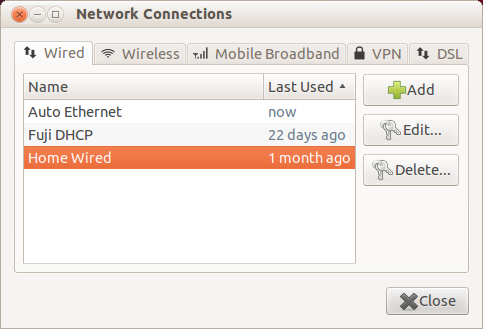
This is the opening screen of the network manager. You will notice that we are looking at the page for Wired connections. There are also tabs for Wireless, Mobile Broadband, VPN, and DSL. For this talk we are only going to deal with the wired and part of the wireless tab.
Next lets look at the entry Auto Ethernet when you choose to edit it.
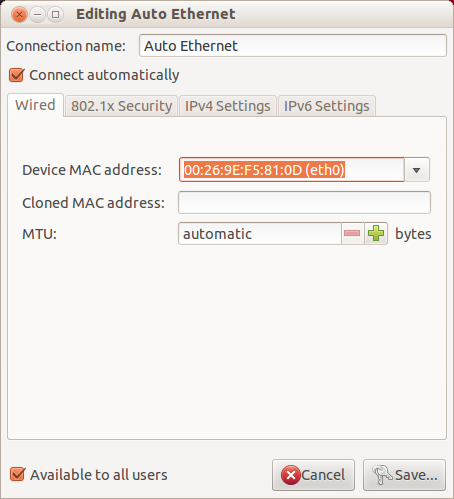
This tab is displaying the Device MAC address:. This is a hardware serial number which is supposed to be globally unique. I say supposed to be because some modems allow you to set the MAC Media Access Control address.
The next item of interest is the MTU. This is a packet size setting, which is normally best left to Automatic because the maximum transmission unit (MTU) is not needed except for some uses by a modem.
Now we will look at the IPv4 page.
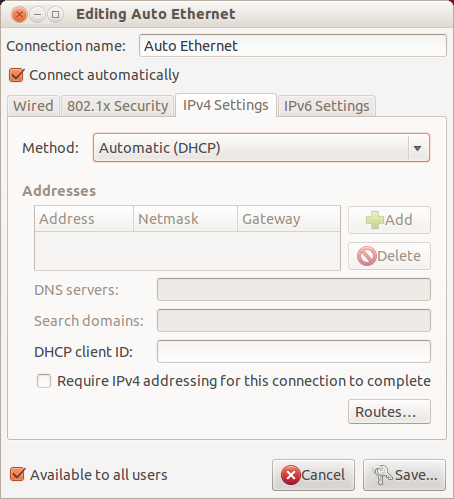
This page is where we specify how the ip address, gateway, DNS, and search domains are set. In this example you will notice the method is set for Automatic (DHCP). By using Dynamic Host Configuration Protocol (DHCP) we let the computer decide what values to use when connecting to the network. This method is convenient when the network routers are set up correctly.
But suppose you want to use fixed values for your network addresses. In many businesses it is common to use fixed IP values for the servers. So here is a page showing the setup for a Static IP.
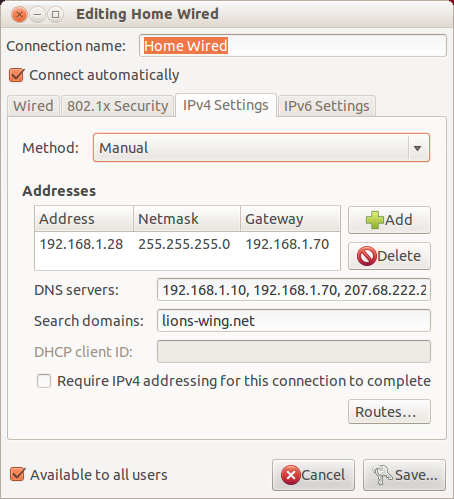
Let have a look at the items on this page one by one:
Method: Manual This specifies that we are going to be entering the values manually.
Addresses: This is the section which contains three fields of interest.
Address: 192.168.1.28 This is the IP address this computer will use.
Netmask: 255.255.255.0 This tells the network how many addresses are use on this Subnetwork.
Gateway: 192.168.1.70 This is the computer that allow access to the addresses outside the network. Often this Gateway is the address of the computer that is used to send packets out of the local network.
DNS Servers: 192.168.1.10 192.168.1.70 … This is a list of which computers provide Domain Name System (DNS). These addresses are listed in the order of importance.
Search domains: lions-wing.net This is the domain of the computer.
Networking on the Command line
Now we have see how to setup the network when we have a graphical interface. But what happens if we only have a command line.
In this tutorial we will be combining troubleshooting and network configuration so hang on for a wild ride. But first let me say that this is only my take on how to perform the tasks.
I am going to use a series of question and answers because that is the best method I know for troubleshooting network issues. I will assume you have logged into the computer and have a bash shell prompt. I am going to use the devices eth0 for a wired connection and wlan0 for a wireless connection.
Is the network connected?
First step is to check if you have a working connection. To do this we will start by looking for an IP address.
or
will display IP information. If you were looking for a wireless IP address use wlan0 instead of eth0.
OK I have an IP address do I have a route?
Checking for a route to the gateway use
or
I have a route, do I have a Name Server?
will display the name server information.
How can I tell if I have any network cards available
will display the network cards, especially the wireless cards. In the future the command will be iw list but that does not work yet on my network card.
How can I set a static IP address for eth0
or
will set eth0 to the ip address 192.168.2.2 with a netmask of 255.255.255.0/24.
How can I set a gateway IP address for eth0
or
Sets the gateway for the eth0 card to eth0.
How to check if DNS is working
This command will attempt to convert the name www.google.com to an IP address. If DNS is working you will get back an IP address. If this command fails, you need to assign some nameserver addressed in the field /etc/resolv.conf.
This will attempt to use the name server 8.8.8.8 to look up the IP address of Google. This is google’s name server so we would hope it knows where to find Google.
How to check if you can access the internet
The ping command allows you to sent a simple packet to a computer which responds by returning the ping. In the first case you are using a name server to look up www.google.com and then send a ping request. In the second case, you are supplying the IP address so no name server look up is needed.
Is the gateway computer alive
This allows you to make sure your computer can talk to the gateway computer. Sometimes DHCP will give you a gateway address which is not active or not in your subnet.
Who owns that Internet name
When you get a strange link in an email, you can check if the owner of the name is someone you want to talk to. If there is no information available for the URL it is a good bet this is a malware address.
How fast is my network connection
Here are three web sites which can help answer this question
This last site What Is My IP has a number of tools to look up more information on the Web.
Example of a Packet transfer
Data Flow from End-to-End
Assume that you are sending an email. Email uses a protocol called SMTP (Simple Mail Transfer Protocol) to deliver the email to the remote host. SMTP comes under Application Layer. The data will be passed to TCP (Transport Layer). TCP will split the data into small units. It will add TCP header information to each unit. Now this unit of data along with TCP Header is called a TCP-Segment. TCP sends it to IP (Network Layer). IP will add its own header information to the TCP-Segment. The unit of TCP-Segment along with the IP Header is called an IP-Datagram. IP sends the Datagram to Ethernet (Link Layer). Ethernet will add its own header information to the IP-Datagram. The unit of IP-Datagram along with the Ethernet Header is called an Ethernet-Frame.
Now, TCP may receive data from one or more applications. To identify each one of them uniquely it will use a number called PORT number (16-bit). Using 16-bit we can have port no. from 0 to 65535. Ports are classified as well-known ports (used by servers - ranging from 0 to 1023) and ephemeral ports (used by clients - greater than 1023). The 4.12 Note on RFCs/STDs/FYIs/BCPs 13 assignment of port numbers is handled by IANA (Internet Assigned Numbers Authority). A single server may provide more than one services each distinguished by the port number. For e.g. a server can provide ftp (Port#21), http (Port#80), telnet (Port#23) all at the same time. Thus a TCP Connection is identified by 4 parameters:
{Source IP Address, Source Port Number, Destn. IP Address, Destn. Port Number}(IP Address, Port Number) pair is also called as SOCKET. Thus each TCP connection can be uniquely identified by two sockets: source socket and destination socket. Remember a SOCKET identifies one end of a TCP connection.
IP may receive data from one or more sources like TCP, UDP, ICMP, IGMP etc. . . To distinguish each one of them it uses a unique number called protocol number [8-bit protocol field in the IP Header]. In Unix machine you can find the protocol numbers in /etc/protocols file. For e.g. the value of protocol number for TCP is 6 and that of UDP is 17.
Ethernet may receive data from one or more sources like IP, ARP, RARP etc. . . To distinguish each one of them it uses a unique number called frame type [16-bit frame type field in Ethernet Header].
Thus, at the remote end, the Ethernet receive the frame, check its frame type and demultiplex the datagram to either IP/ARP/RARP. If IP receives the datagram, based on the 8-bit protocol field, it demultiplex the data to either TCP/UDP/ICMP/IGMP. If TCP receives the data, based on the 16-bit port number, it demultiplex the data to the corresponding application.
ICMP, IGMP make use of IP Datagram Delivery Service & ARP, RARP make use of Ethernet for sending ARP/RARP packets. Thus IP may receive data from TCP/UDP/ICMP/IGMP (other sources are also possible, but that is not important here).
This document GNU/Linux Networking Tutorial for Newbies is a good source of information, although it is detailed.
Linux Networking Books
Linux Networking Clearly Explained
Linux Networking Clearly Explained deals with setting up a Modem and other low level networking issues.
Your Linux networking journey starts with the fundamentals— setting up your modem and creating an Internet connection. This chapter fully surveys the knowledge you will need to create such a connection successfully.
— Bryan Pfaffenberger Linux Networking Clearly Explained
This book covers the details needed for PPP, and modem communications. Even though this is no longer needed by most people, it is still of use to some, so I included it here.
Linux Netorking Cookbook
Linux Networking Cookbook is a how to from O’Reilly
So there you are, staring at your computer and wondering why your Internet connection is running slower than slow, and wishing you knew enough to penetrate the endless runaround you get from your service provider. Or, you’re the Lone IT Staffer in a small business who got the job because you know the difference between a switch and hub, and now you’re supposed to have all the answers. Or, you’re really interested in networking, and want to learn more and make it your profession. Or, you are already knowledgeable, and you simply have a few gaps you need to fill. But you’re finding out that computer networking is a subject with reams and reams of reference material that is not always organized in a coherent, useful order, and it takes an awful lot of reading just to figure out which button to push.
— Carla Schroder Linux Networking Cookbook
This book has several interesting chapters, for those of you dealing with sophisticated networking this book has answers and explanations.
Here is a list of the sections in the book.
Introduction to Linux Networking
Building a Linux Gateway on a Single-Board Computer
Building a Linux Firewall
Building a Linux Wireless Access Point
Building a VoIP Server with Asterisk
Routing with Linux
Secure Remote Administration with SSH
Using Cross-Platform Remote Graphical Desktops
Building Secure Cross-Platform Virtual Private Networks with OpenVPN
Building a Linux PPTP VPN Server
Single Sign-on with Samba for Mixed Linux/Windows LANs
Centralized Network Directory with OpenLDAP
Network Monitoring with Nagios
Network Monitoring with MRTG
Getting Acquainted with IPv6
Setting Up Hands-Free Network Installations of New Systems
Linux Server Administration via Serial Console
Running a Linux Dial-Up Server
Troubleshooting Networks
Written by John F. Moore
Last Revised: Tue 01 Sep 2020 08:10:06 PM EDT

This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 3.0 Unported License.
